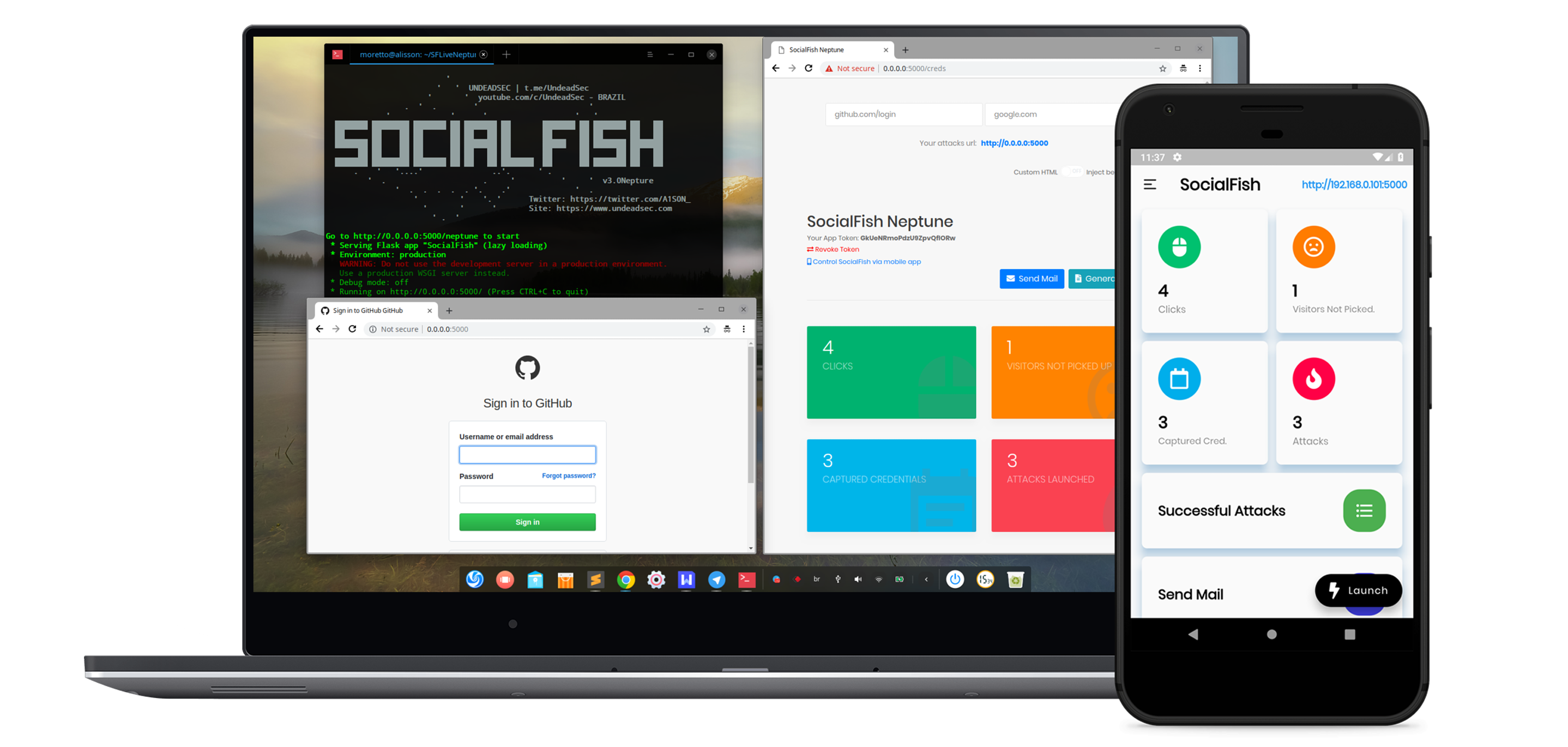
This enhanced version of SocialFish has been significantly improved by the Tech Sky Security Research Team to provide advanced capabilities for ethical security testing and research purposes.
- 🎯 Universal Website Cloning - Clone any modern website with high fidelity
- ⚡ Advanced Resource Capture - Automatically downloads all website assets including images, CSS, JavaScript, and fonts
- 🔒 Enhanced Functionality - Cloned websites maintain full functionality with working forms and interactive elements
- 🛡️ Improved Reliability - Advanced retry mechanisms ensure successful cloning even with protected sites
- 📱 Mobile & Desktop Compatibility - Works seamlessly across all device types and screen sizes
- 🎨 Perfect Visual Reproduction - Maintains exact styling and layout of original websites
- ⚙️ Smart Resource Management - Intelligent handling of dynamic content and lazy-loaded resources
- 📊 Comprehensive Logging - Detailed capture statistics and debugging information
This version includes significant improvements over the original SocialFish:
- Advanced Cloning Engine - Handles modern web applications with dynamic content
- Intelligent Resource Discovery - Finds and downloads all website dependencies automatically
- Enhanced Form Processing - Ensures login forms and interactive elements work properly
- Dynamic Content Support - Captures JavaScript-loaded content and framework-based sites
- Improved Error Handling - Robust fallback mechanisms for reliable operation
- Better Performance - Optimized resource management and faster cloning speeds
Are you looking for SF's mobile controller? UndeadSec/SocialFishMobile
Are you looking for SF's old version(Ngrok integrated) ? UndeadSec/SociaFish/.../sharkNet
Visit the wiki for more details.
Setup instructions here.
How to run with Docker?
You need to run:
docker compose up- Alisson Moretto, Twitter: @UndeadSec, GitHub: @UndeadSec
- Vandré Augusto, Twitter: @dr1nKoRdi3, GitHub: @dr1nK0Rdi3
- Fernando Bellincanta, Twitter: @ErvalhouS, GitHub: @ErvalhouS (Documentation)
- Tech Sky - Security Research Team - Advanced cloning engine and enhanced capabilities
- Community Contributors - Bug reports, feature requests, and testing support
This enhanced version is designed exclusively for:
- Security Research - Understanding web application vulnerabilities
- Educational Training - Learning about phishing attack vectors
- Penetration Testing - Authorized security assessments with proper consent
- Red Team Exercises - Simulating attacks in controlled environments
This tool must NOT be used for:
- Illegal Activities - Any form of unauthorized access or fraud
- Malicious Attacks - Real-world phishing campaigns against individuals
- Identity Theft - Stealing credentials or personal information
- Financial Fraud - Any activities involving monetary theft or deception
- Harassment - Targeting individuals without their knowledge or consent
Before Using This Tool:
- Obtain Written Permission - Always get explicit authorization before testing
- Document Your Testing - Maintain clear records of all security research activities
- Respect Privacy - Never capture or misuse real user credentials
- Follow Local Laws - Ensure compliance with applicable cybersecurity regulations
- Use Test Environments - Prefer isolated testing environments when possible
During Security Research:
- Limit Scope - Only test systems you are authorized to assess
- Protect Data - Securely handle any captured information during testing
- Report Responsibly - Follow responsible disclosure practices for any vulnerabilities found
- Clean Up - Remove all testing artifacts after completing assessments
- Credential Handling - This enhanced version includes advanced credential capture capabilities for authorized testing only
- Data Protection - Ensure all captured test data is properly secured and disposed of after research
- Network Security - Use appropriate network isolation during testing activities
- Access Control - Restrict tool access to authorized security researchers only
TO BE USED FOR EDUCATIONAL AND AUTHORIZED SECURITY RESEARCH PURPOSES ONLY
The use of this enhanced SocialFish version is the COMPLETE RESPONSIBILITY of the END-USER. The original developers and the Tech Sky Security Research Team assume NO liability and are NOT responsible for any misuse or damage caused by this program.
This enhanced version includes powerful capabilities that must be used responsibly. Users are required to:
- Comply with all applicable local, state, and federal laws
- Obtain proper authorization before conducting any security testing
- Use the tool only in authorized, controlled environments
- Respect the privacy and security of others at all times
"DISCLAIMED. IN NO EVENT SHALL THE COPYRIGHT HOLDER OR CONTRIBUTORS BE LIABLE FOR ANY DIRECT, INDIRECT, INCIDENTAL, SPECIAL, EXEMPLARY, OR CONSEQUENTIAL DAMAGES (INCLUDING, BUT NOT LIMITED TO, PROCUREMENT OF SUBSTITUTE GOODS OR SERVICES; LOSS OF USE, DATA, OR PROFITS; OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER IN CONTRACT, STRICT LIABILITY, OR TORT (INCLUDING NEGLIGENCE OR OTHERWISE) ARISING IN ANY WAY OUT OF THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE."
Taken from LICENSE.
We encourage responsible contributions to SocialFish! Please check out the Contributing to SocialFish guide for guidelines about how to proceed.
For Enhanced Version Contributions:
- All contributions must align with ethical security research principles
- Features should enhance legitimate security testing capabilities
- Documentation must include appropriate usage warnings and guidelines
Join us in making cybersecurity research more effective and accessible!
This project adheres to No Code of Conduct. We are all adults. We accept anyone's contributions. Nothing else matters.
However, for this enhanced version, we expect contributors to:
- Respect the ethical boundaries outlined above
- Contribute features that support legitimate security research
- Help maintain the tool's focus on educational and authorized testing purposes
For more information please visit the No Code of Conduct homepage.
The Tech Sky - Security Research Team is dedicated to advancing cybersecurity through responsible research, education, and tool development. Our mission is to help security professionals better understand and defend against emerging threats through ethical testing methodologies.
Contact: For questions about the enhanced features or responsible usage guidelines, please reach out through appropriate security research channels.